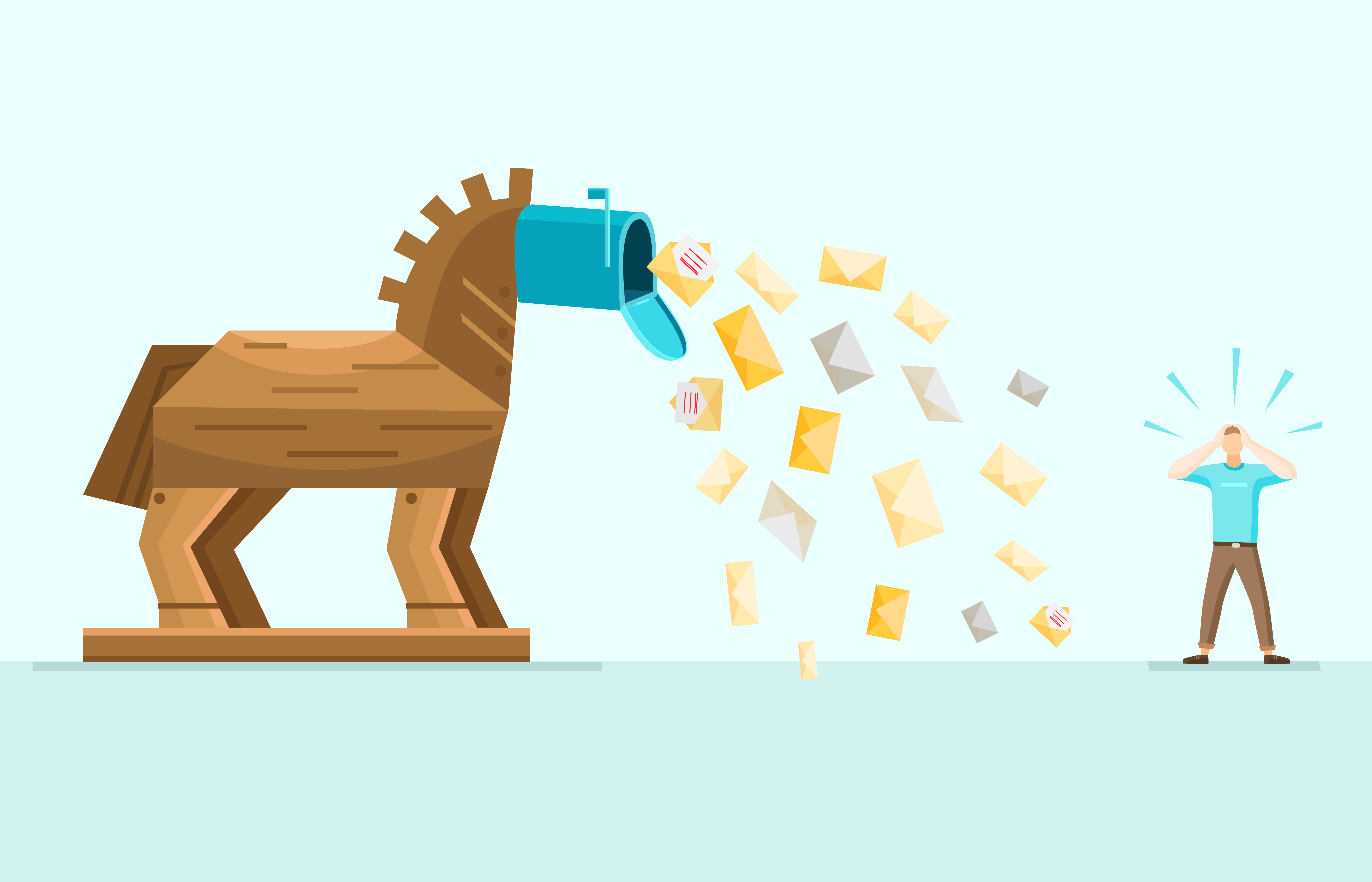
Everything You Should Know About Trojan Emails
Cyber-attacks are at an all-time high. Hackers typically use different techniques to access victims’ data. Trojan emails are one such method. These emails come with malicious software or code, which at first glance, appears legitimate but is meant to assume control of your computer. Often, Trojan emails trick users into downloading malicious programs that are purported to be normal and safe.
Trojans are usually disguised, thus making it difficult for computer users to detect them. Even so, their impact can be severe. Also known as Trojan horses, cybercriminals have used this type of malware for more than two decades. However, the popularity of Trojans has grown further due to an increase in the opportunities for downloading free software and programs online.
According to cybersecurity experts, Trojan emails are among the most dangerous and common forms of malware in existence. They pose a threat to whole networks as well as individual devices. Unlike viruses, Trojan horses cannot replicate. Likewise, a Trojan can only infect your network or devices after you execute it.
Types of Trojan Emails
Generally, there are five main types of Trojan malware. When sent to victims via email, they can be categorized as Trojan emails.
-
Destructive Trojans
These Trojan horses are designed to crash your devices, delete or modify files, corrupt data. In severe cases, they can format your computer disks, thus deleting your data permanently.
-
Resource Appropriation & Identity Trojans
Email Trojans in this category are designed to appropriate your devices’ identity and resources. As a result, the devices will start performing automated spamming. They may also be used to mine cryptocurrencies or as a proxy for illicit activities.
-
Theft and Ransom
Some Trojans are specially created to either steal electronic money or extort money from Internet users using ransomware. If you are a victim of Trojan emails that end up locking your device, you might be asked to pay the malware operators before they unlock your devices. Often, these cybercriminals pose as law enforcement officers or security agency employees.
-
Data Theft Trojan Horses
Some Trojan emails are sent out to help hackers steal their victims’ data. Data theft Trojans target intellectual property, commercial information, personal data, and everything in-between.
-
Spying and Surveillance Trojans
Hackers are increasingly leveraging Trojan emails to spy on unsuspecting Internet users. Keystroke logging, accessing users’ webcams, and the remote control of computers are some typical threats that spying and surveillance Trojans pose.
How are Trojan Emails Used to Infect Your Devices?
To understand how Trojan emails are used to spread malware, you should look back at instances when you received emails from familiar people. Often, these emails have links or attachments that look genuine. If the email is from cybercriminals and you end up opening the attachment, malware may get installed on your device. With time, the malware can spread to other files or the entire network, thus putting all your data at stake.
Typically cybercriminals leverage weaknesses in outdated software or apps to intrude your system. Human error also contributes significantly to the spread of Trojan emails. The seemingly innocent software updates, routine installations, or add-ons could be a front for spreading malware. This highlights the significance of always being on the lookout for malware sent via email.
Protecting Yourself Against Email Trojans
There is so much that you can do to protect yourself against the devastating impacts of Trojan emails. Generally, computer security starts with installing and running a network security suite. Diagnostic scans can go a long way in sealing loopholes that cybercriminals would hitherto exploit. You can also automate the scans so that they run automatically.
Ensure that you update your OS’s software whenever software companies avail updates. Cybercriminals prefer exploiting security holes that are inherent in outdated software. Besides OS updates, you should also be on the lookout for updates on other programs installed on your computers. Since Trojan emails spread malware that can cause data corruption, ensure that your files are regularly backed up. This way, sensitive data won’t be lost if Trojan horses infect your computer.
The surest way of preventing Trojan emails from infecting your computers is being careful with links and attachments that are sent via email. Always scan the links to detect malware before opening them. Also, don’t open links in emails sent to you unless you’re sure that they are from legitimate sources. If possible, avoid opening unsolicited mail from people that you don’t know. NuEduSEC not only offers high-end threat protection tools, but its experts can also teach you how to protect yourself from Trojan emails. Contact them today to learn more.